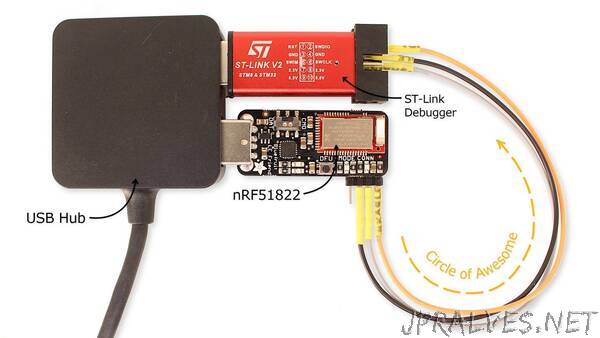
“Recently, while conducting an assessment for a product based on the nRF51822 System on Chip (SoC), I found my target’s debug interface was locked – standard stuff. Reading up on the nRF51 series SoCs revealed that this is how these chips are designed. It’s always possible to perform a full memory recovery/dump, even if read back protection is enabled.
I wanted to build on what others have discovered, extending the attack to completely and automatically bypass the memory protection mechanism offered by these SoCs. Beyond reading memory, I also wanted to unlock the device to support interactive debug sessions with my target.
This post outlines the theory behind the shortcomings of the debug interface memory read back protection mechanism and introduces a simple tool (nrfsec), to automate the entire process using low-cost debugging hardware.”