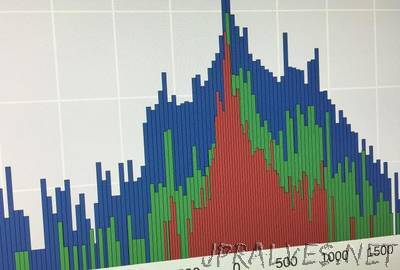
“By analyzing network traffic going to suspicious domains, security administrators could detect malware infections weeks or even months before they’re able to capture a sample of the invading malware, a new study suggests. The findings point toward the need for new malware-independent detection strategies that will give network defenders the ability to identify network security breaches in a more timely manner. The strategy would take advantage of the fact that malware invaders need to communicate with their command and control computers, creating network traffic that can be detected and analyzed. Having an earlier warning of developing malware infections could enable quicker responses and potentially reduce the impact of attacks, the study’s researchers say.”